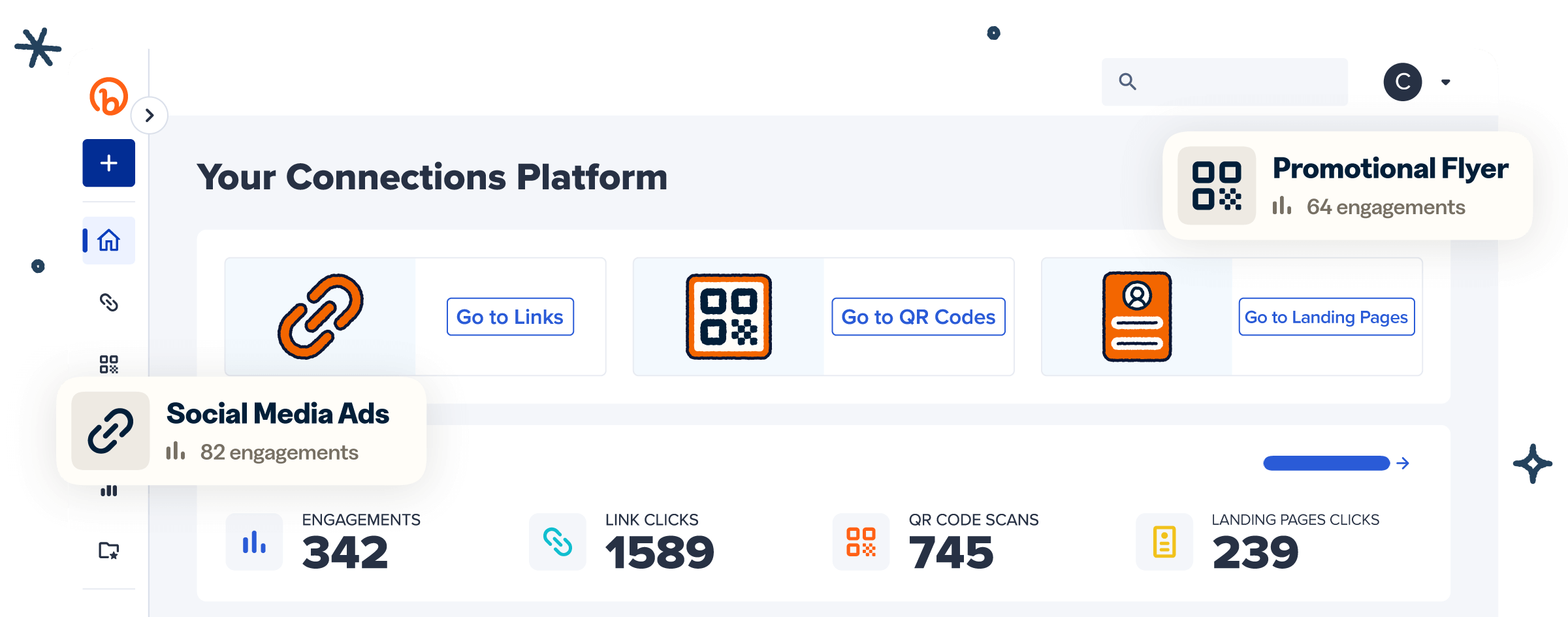
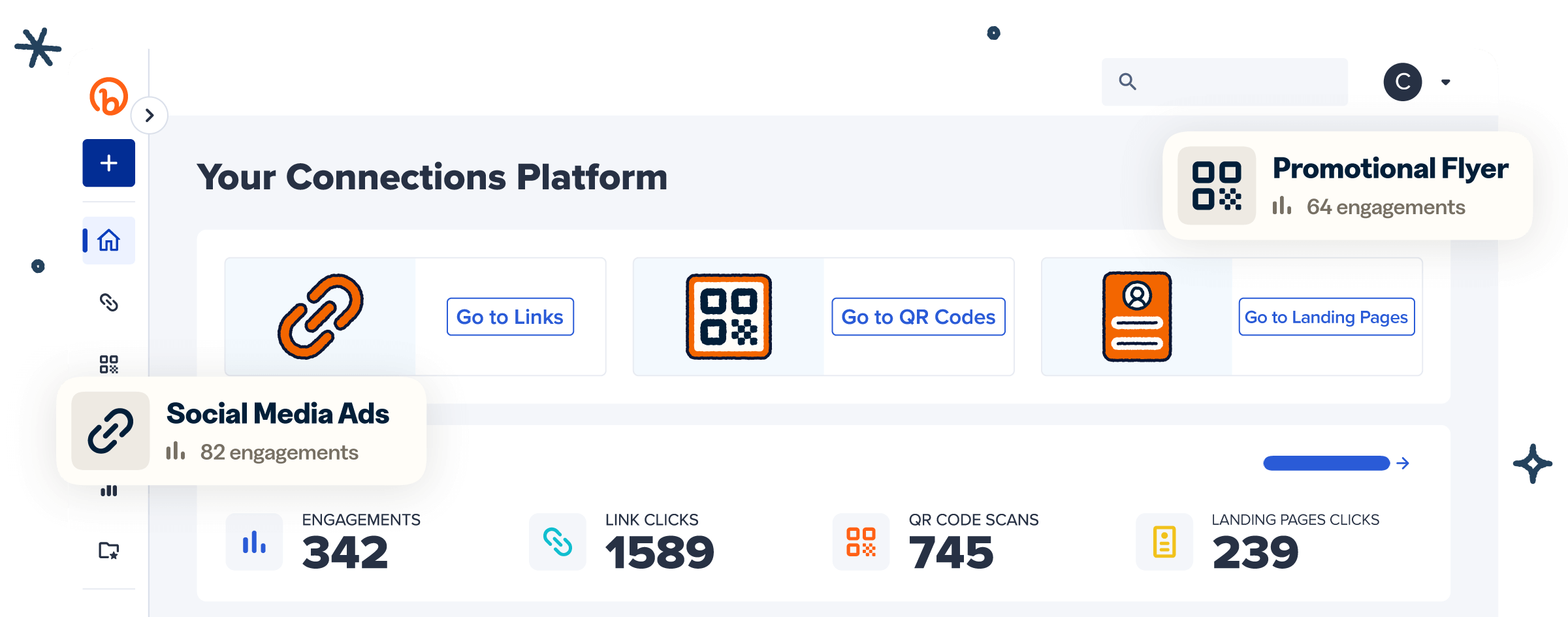
More than a link shortener
Knowing how your clicks and scans are performing should be as easy as making them. Track, analyze, and optimize all your connections in one place.
The first step in these challenges is usually reverse-engineering the .1zip header. Typically, the format includes: A sequence (e.g., 1ZIP ). Metadata for file count and individual file lengths. Filenames followed by the raw File Content . 2. Identifying the Vulnerability
Creating a symlink inside the archive that points to a sensitive system file. When the service "updates" or "reads" the file, it interacts with the system target instead. 3. Exploitation (General Example)
A service or binary that parses a custom archive format called .1zip . lhfs_1zip
The "lhfs" component suggests the challenge interacts directly with the host's file system. Common attack vectors include:
While a specific "official" write-up might be hosted on private CTF platforms (like Hack The Box or specific university labs), the challenge typically revolves around exploiting a implementation that handles .1zip files. Challenge Overview The first step in these challenges is usually
If the extraction tool doesn't sanitize filenames, you can use ../ to write files outside the intended directory (e.g., overwriting .ssh/authorized_keys or /etc/passwd ).
Upload or pass this file to the lhfs binary. If vulnerable, it will attempt to "extract" the file to that path or read from it, often leaking the contents in the process. Common Mitigation Filenames followed by the raw File Content
If the goal is to read a flag located at /flag.txt , the exploit usually involves crafting a malicious .1zip file: Manually create a file with the 1ZIP header. Payload: Set the filename field to ../../../../flag.txt .

Knowing how your clicks and scans are performing should be as easy as making them. Track, analyze, and optimize all your connections in one place.