Download Шіщљш±щѓш± - (18) Txt
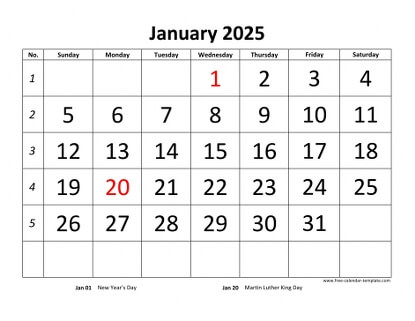
The "18" in the filename wasn't a version number. It was the date. April 18th.
Elias looked at his watch. It was April 17th, 11:58 PM. He realized then that the file wasn't a record of the past—it was a set of instructions for what was about to happen to him in exactly two minutes. Download ШіЩЉШ±ЩЃШ± (18) txt
He spent four hours writing a custom script to bypass the encoding errors. When the file finally clicked open, it wasn't a list of passwords or a manifesto. It was a single, long-running log of a sensor. Ambient temp 72°F. Humidity 40%. 14:02:05: Pulse detected. 62 BPM. 14:02:10: Pupil dilation confirmed. Oxygen saturation 98%. The "18" in the filename wasn't a version number
As the clock ticked toward midnight, his computer screen flickered, and the webcam's small green light—the one he’d covered with tape months ago—began to glow through the plastic. Elias looked at his watch
Elias, a data recovery specialist, found it buried in a deep-partition sector of a "clean" drive he’d bought at a liquidation auction. The server (or Sirfar , as the garbled text transliterated from Arabic) shouldn't have been there. It was only 4KB, but it refused to open with standard editors.
The filename was a digital ghost—a string of Cyrillic and Arabic characters that didn’t belong together: Download ШіЩЉШ±ЩЃШ± (18).txt .
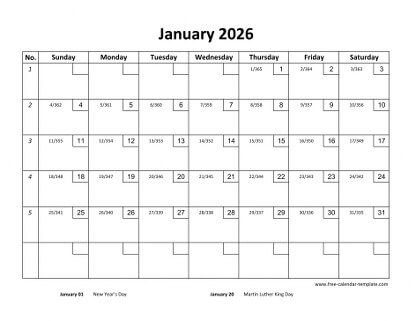
Elias frowned. The data looked like medical telemetry. He scrolled to the bottom, expecting the log to end with a system crash. Instead, he found a line that chilled him: Subject identified: Elias Thorne. 23:59:59: Proximity: 0.5 meters. 00:00:00: Status: Download Complete.